Live forensics
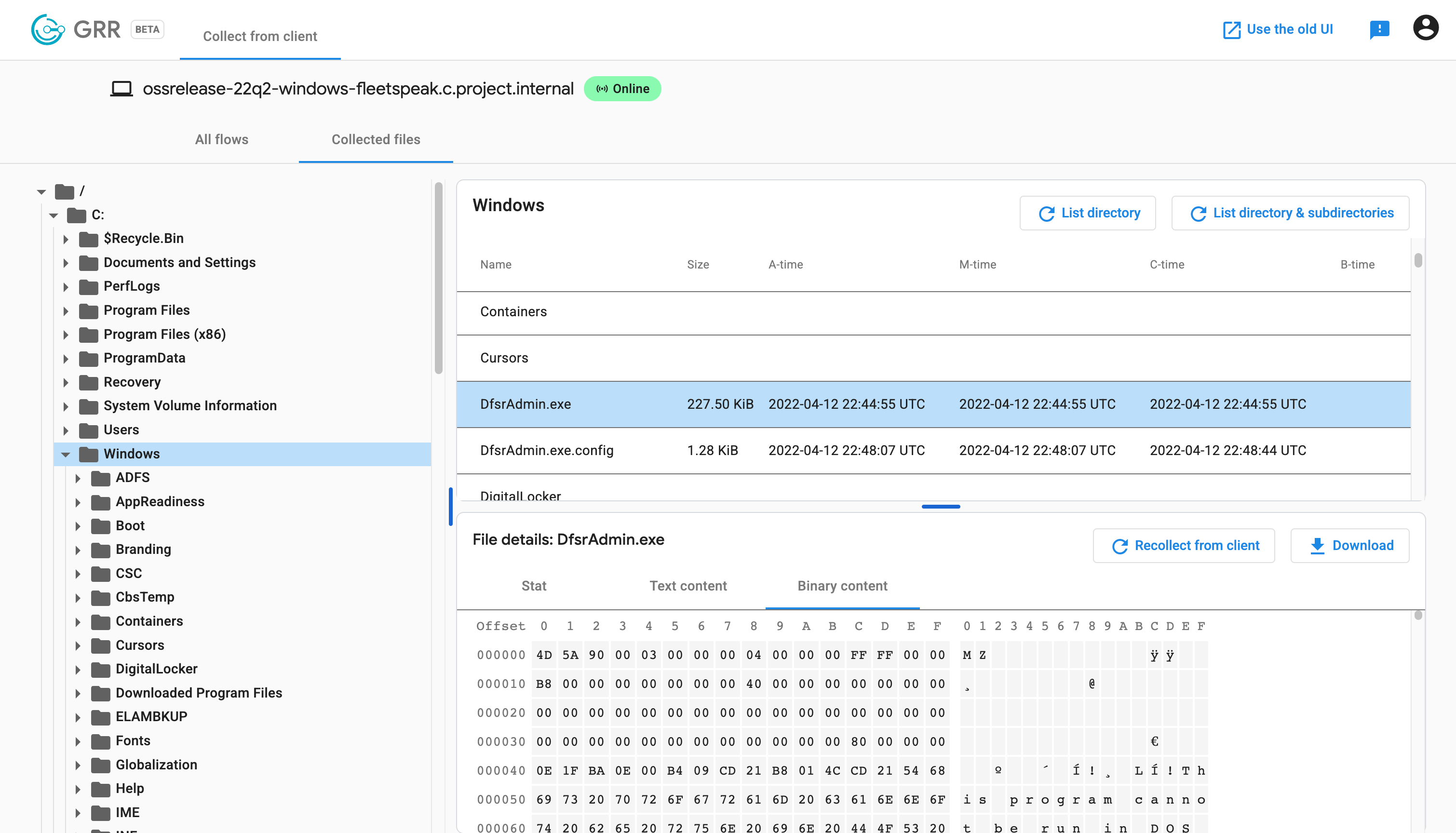
Search, list, and collect files
Search for files based on criteria like path, regex and content matching. List directories or the whole hard disk timeline. Collect the contents of regular files and special OS primitives like devices and alternate data streams. Parse NTFS file systems to read locked files on Windows.
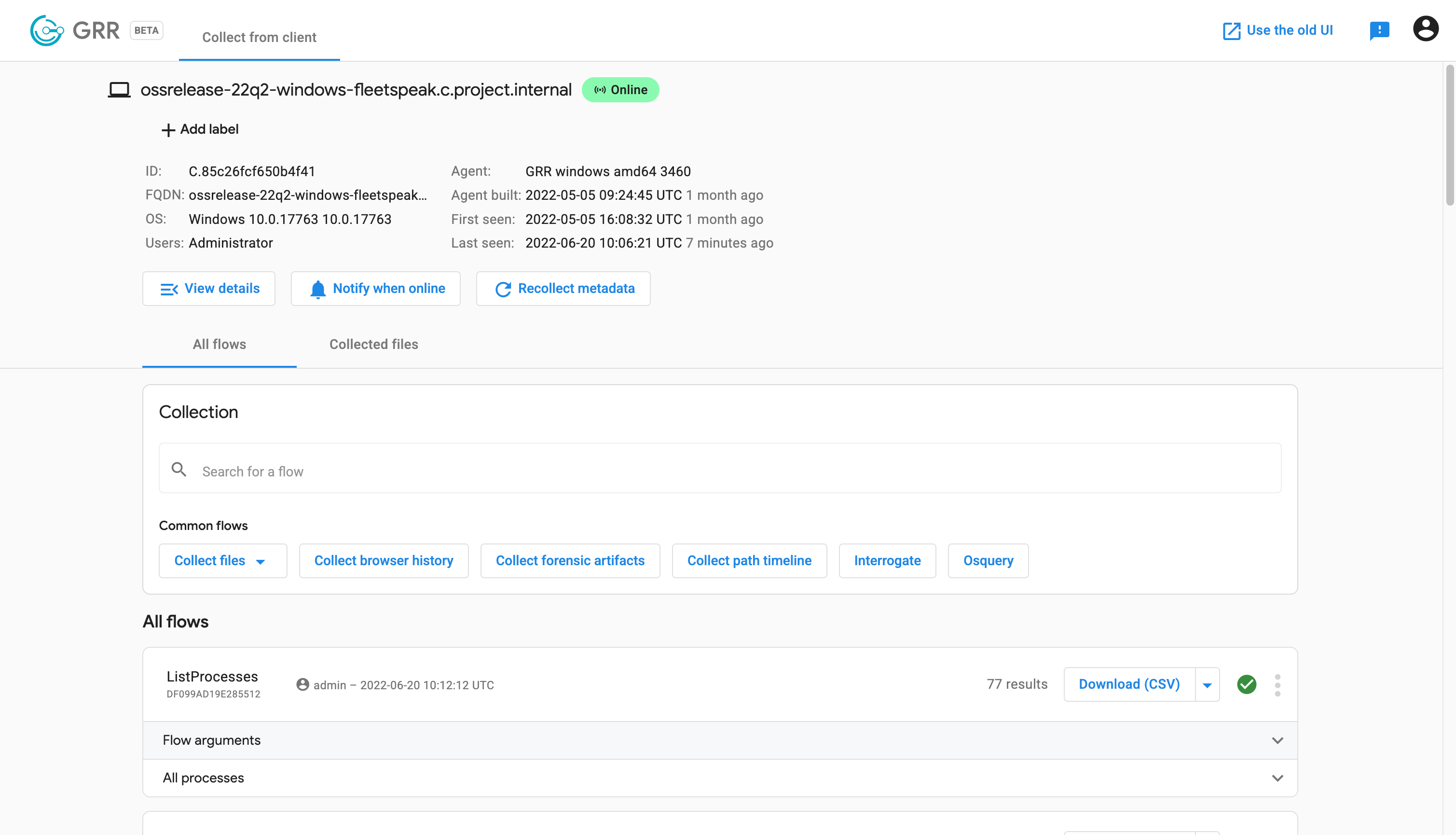
List processes, network connections, and named pipes
Get insights into what's happening on an endpoint. Search for and list processes, enumerate open network connections and list special OS primitives like named pipes.
Collect forensic artifacts, run osquery
Use predefined recipes for forensic data collection (ForensicArtifacts), create your own to quickly and reproducibly gather forensic evidence, and send queries to osquery.
Live process memory analysis
Scan the memory of running processes for indicators of compromise with yara and dump the memory pages for further forensic analysis.
At Scale
Check & collect data on thousands of endpoints
Schedule Hunts on your whole fleet and offline endpoints will pick up the hunt when you’re back online.
Low latency communication
Send commands to endpoints and receive data collection results in seconds through Fleetspeak.
Periodic fleet checks
Configure cron jobs to repeat hunts periodically, turning one-off investigations into regular checks.
For security teams of any size
Enable advanced features like multi-party authorization with approvals and pluggable authentication when your security team grows.
Anywhere
Deploy agents to all major operating systems
Run agents on Debian, Ubuntu and CentOS-based Linux distributions, macOS and Windows.
Pre-packaged, single-file installers for all operating systems
Download the pre-packaged installer from the GRR web application after setting up your installation.
Secure communication between client and server
Agents have the GRR server's address and certificate baked in for secure communication. All communication is encrypted.